Securing device access to the server
To grant end-users application access to the server using their mobile/computer device, the main security measures revolve around user and device authentication. OAuth 2.0 is the most used authorisation and authentication framework. It is being used by firms like Google and Facebook. MQTT protocol supports the following authentication processes:
1. Username and password or access token
MQTT protocol develops a UTF-8 encoded string user name and a binary data-type password, where each field can be expanded up to 65,535 bytes maximum. The client, i.e., the user, needs to provide a valid username and password to get access from the MQTT broker. Many systems accept passwords instead of tokens, using which the broker can assess the validity, signature and access rights of the user.
2. One-time password (OTP)
It is often used for a two-step security, wherein registered devices need to verify their eligibility of access based on an OTP received on the device.
3. Biometrics
This mode of authentication is gaining popularity. Many smartphones and smart devices have introduced fingerprint scanners for access. IoT systems are also incorporating biometric authentication procedure to improve the security measures. Some of the newer bio-authentication processes include facial scan and eye scan. Hemnani informed, “Like smartphones, IoT devices will also implement fingerprint sensor soon. That way, only an authorised user will be able to access the IoT device.”
Security at the edge and component level
Field devices where the data is being generated by the sensors have a temporary storage capacity, which queues the data to be pushed to the server. The major security threats that device storage faces include tampering of the telemetry data, tampering of the cached content and alteration of the device operating system. Simple security options include digital signatures, message authentication code (MAC) and resource access control. Dr Amarjeet Singh, co-founder and CTO, Zenatix Solutions, explained the process of securing a server from a rogue edge device which might have been physically taken over by a hacker: “A rogue device intruding into an IoT system tries to overload the server by sending an abnormally high amount of data. A security measure taken for server configuration is to limit the amount of data package the server will accept from each device at a given time interval. If any device is transacting higher data than the threshold too often, it is barred from the network.” Device gateways that channel sensor data to the server can be secured by BitLocker. Talking about securing the data in embedded components, Kumar Bhaskar, technology lead of Beyond Evolution, a company working on IoT devices, said, “Components of IoT systems use very limited resources in the form of embedded hardware like a small chip, sensor, controller and RAM. So data is embedded in the controller’s memory in encoded or symbolic format. Once the microcontroller is coded, it is locked. So, firstly the data cannot be fetched by any means from the controller. Additionally, the data itself will not be in a readable format.”
Software as security suites
Implementing security software has been a staple safety procedure for IoT systems. Here, Sharma shared, “Mostly software solutions are available to secure firmware.” Gartenberg added, “Success of this transformation largely depends on choosing the right IoT software and service provider who can not only catalyse this transformation by understanding business needs but also provide services and software built with security and compliance as major design considerations.” Talking about Microsoft’s contribution to IoT security via software, he added, “The Microsoft Azure IoT Suite builds in security measures by design, enabling secure asset monitoring to improve efficiencies, drive operational performance to enable innovation, and employ advanced data analytics to transform businesses. With its layered approach towards multiple security features, and design patterns, Azure IoT Suite helps deploy an infrastructure that can be trusted by any business.”
What’s the future
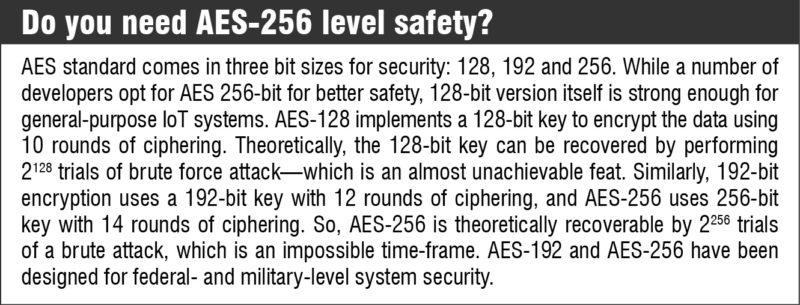
In the coming two to three years, even newer security upgrades will be available and the systems will have to be updated. Code signing abilities with higher levels of encryption may be a step forward to secure the devices.
As regards security practices for the IoT, Dr Bhatnagar said, “A security operations centre needs to be established to monitor threats in a proactive manner while detecting and tracking signatures of divergent activities. On the tactics side, sanitise your operational environment by deploying patches, keeping segmented offline back-ups, conducting audits and deriving visibility into your core and peripheral networks. If a malware breaches your first layer of defence, you should be able to know where it is and what exactly it is doing. Most importantly, ensure that everyone in your organisation understands the collective responsibility they bear for cybersecurity.” Experts feel that endpoint security monitoring will see the maximum advancements in the next ten years. Data analytics, machine learning and artificial intelligence will play a big role in the prediction of attacks and suspicious activities. The current movement towards a common IoT standard will influence the future security trends. We will see better encryption capabilities and more evolved authentication and authorisation processes.












